Humans are often their own worst enemies. We’re flawed beings, destined to learn through our mistakes, to stumble as we grow, fail as we achieve. This is no less true in the world of network security. Equal in danger to malicious actors are accidental actors: those that inflict damage not through malign intent, but negligent behaviour. Tragedies result from both action and non-action; of what we decide to do and what we fail to do, or, at least, fail to notice.
We’re negligent when we’re too busy or preoccupied to take notice: a fitting description for 2020 and most of 2021. In the wake of the pandemic, companies were forced to transform into digital-first companies, realigning infrastructure to accommodate distributed workforces. This meant more apps, expanded network access and, consequently, a greater possibility of negligence. Employees unaccustomed to remote work have had to grow accustomed to new software and ways to access critical information. They’ve had to become aware of cybersecurity, of network attacks, credential theft, all while navigating the thin line between personal and professional, between the comfort of home and the diligence required of work.
Unexamined bad habits, apathy and inattentiveness are now amongst the greatest threats to network security and, by extension, business health and brand reputation.
Negligence: the easy-to-prevent and harder-to
Fortunately, the greatest threats are the most easily prevented (though, unfortunately, what’s easy to prevent is also what’s frequently overlooked). Examples include:
- Weak passwords
- Responding to phishing attacks (or failing to recognise messages as phishing attacks)
- Copies of critical data left in personal cloud-storage accounts
- Using third-party – especially free-to-use – VPNs while accessing accounts
- Failing to update critical software
- Disabling locally installed security software
Many of these are easily solved through regular rehearsal and revision of network security policies and procedures. Others require further education, into the different attack vectors, the dangers of infiltration, and the importance of maintaining local security solutions. Inconvenience is often something employees are keen to avoid; their local computers a sanctum, the interruption of a security solution can feel an interference too-far. But this is where a more honest conversation is also required, a conversation beyond policy. In a distributed network, every access point is a potential doorway. The behaviour of one can impact all, and a behaviour repeated by a few multiplies the threat.
There’s little correlation between job position and negligence. Often, it is the most highly skilled and trusted employees that are responsible. When we repeat a behaviour without consequence, it becomes part of our routine. Lessons are learnt through repercussion.
In our last piece, we spoke about the importance of digital hygiene. Our computers have become our second bodies. What we put into them matters. We have to pay attention to bad habits, and be vigilant and conscientious of our default routines, our susceptibility to occasional laziness and apathy. It’s easy to assume another is responsible for organisational security, that our activities sit behind other defences.
But in a distributed world, everyone has a role to play in preserving network security. Every user, as a human actor, represents a potential point of vulnerability: a gateway that may be accessed through nothing more complained than mislaid keys. A recent article by Nevada IT Solutions identified human negligence as a major cause of data breaches. This makes sense: negligence is the easiest mistake to make, and the easiest vulnerability to leverage.
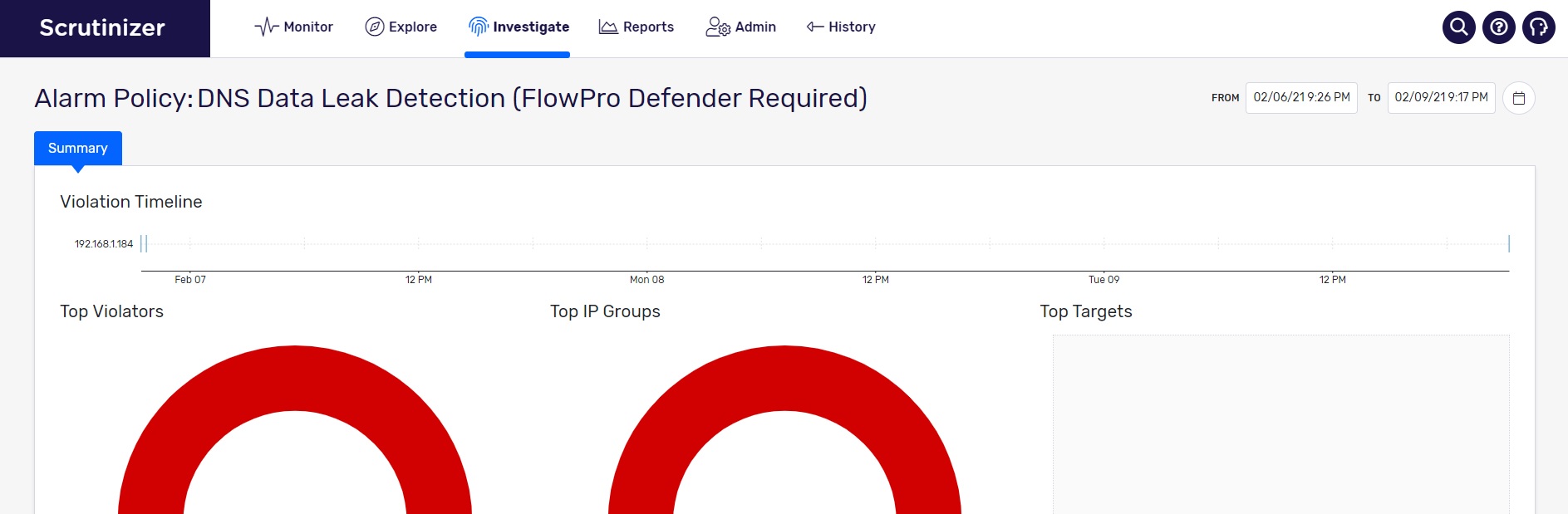
Scrutinizer by Plixer’s role in detecting threats
There are solutions. Better employee awareness allows you to mitigate security threats, but not avoid them entirely. Negligence is, as we’ve pointed out, a very human behaviour, and to an extent unavoidable. Scrutinizer by Plixer – using its new Security Intelligence module – provides secondary defence through machine learning. Amongst other things, Scrutinizer can identify and detect vulnerabilities such as server message block (SMB) associated with a specific source and destination IP address. It rapidly detects and reports deviations of SMB traffic behaviour within the company’s network.
Protecting against another major vulnerability, the loss or misuse of user credentials, Scrutinizer can integrate with Plixer Beacon to enable endpoint visibility. This information allows for a precise and rapid incident response; SOC analysts can detect the actor’s location, operating system, current IP address, device type and MAC address – all within the company’s network.
For more information on protecting against employee negligence – and how Scrutinizer by Plixer and other Plixer solutions can help – contact us today.