Like a schoolteacher intruding upon our late-in-life dreams, ping is an enemy of old we’re keen to forget. Ping issues aren’t regular occurrences these days, but that also makes them dangerous. Preparedness comes from rehearsal. And just because we don’t see an issue doesn’t mean it isn’t still lurking, biding its time to catch us off guard.
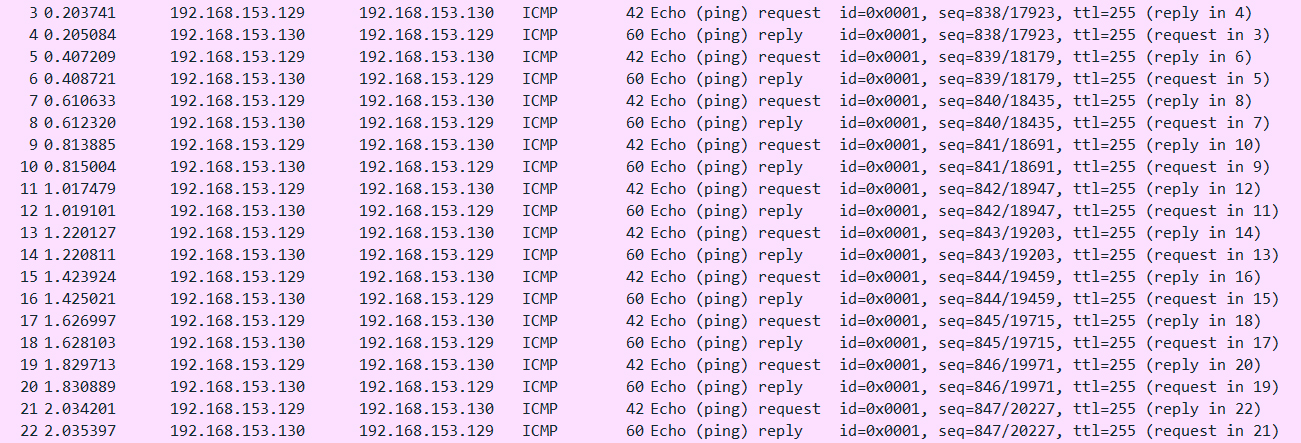
Luckily, unlike the days of old – the era of scratchy phone lines – there are solutions to help us. Ping, officially known as ICMP, is one of the older types of RFC (Requests for Comment). Most often, it’s used to troubleshoot networks by sending out requests for echoes and replies. In the day of LAN networks and on-premises networks, pinging was a useful way to see if devices were talking to one another.
Times have changed, however. On some networks, managers choose to block ICMP traffic: a nuclear alternative to monitoring. But there are reasons to keep ICMP open – and ways to monitor it to keep it secure. Even the infamous Ping of Death has gone the way of the Nokia 3310: modern devices can filter or mitigate ping size before processing fragmented packets.
Monitor ICMP with Scrutinizer by Plixer
The ICMP protocol can be abused, which we’ll discuss later on, but the degree of its vulnerability is determined by whether a monitoring solution is in place. Scrutinizer, a network monitoring and analysis solution by Plixer able to, as the name implies, scrutinise data packets for greater detail and context, provides multiple ways to monitor ICMP. This includes five flow analytics algorithms that help detect suspicious behaviour and misconfiguration surrounding the ICMP protocol:
– ICMP Destination Unreachable.
– ICMP Port Unreachable
– Ping Flood
– Ping Scan
– Large Ping
Let’s look at each in more detail. ICMP Destination Unreachable and ICMP Port Unreachable both identify network issues or attempts to reach down or non-existent services. Ping Flood is designed to protect against ping flooding: a symmetrical ICMP attack in which an attacker performs echo requests to overwhelm a device. The flow algorithm can be tuned to alert prior to this event occurring, with enough bandwidth to overwhelm the targeted device, allowing a network manager to mitigate the attack.
Ping Scan identifies devices or systems that are potentially infected, misconfigured or over a specified threshold of unique device pings. And, finally, Large Ping. The Large Ping algorithm is able to identify Ping-of-Death attacks as well as bad actors learning about your network (an attacker may send larger-than-normal pings to learn the capabilities of a specific network path).
Should you monitor ICMP traffic?
Probably, yes. It’s better to know what’s being attempted on your network than not. Blocking ICMP traffic is a solution, but not an ideal one, as it precludes the benefits that ICMP can provide, and the insight into network security and health. Ultimately, with Scrutinizer by Plixer, it isn’t necessary. The flow algorithms described here are just a few of the comprehensive monitoring capabilities the tool provides. The ICMP protocol can be abused – and traffic even tunnelled through ICMP as a means of data exfiltration – but the likelihood of such attacks succeeding is drastically diminished by Scrutinizer by Plixer. With monitoring, alerting and reporting – and the more complete insight provided therein – network managers stay in control.
For more information on using Scrutinizer by Plixer to monitor ICMP or other types of traffic, contact us today.