In our last piece, we discussed Scrutinizer’s new Network Intelligence module. That module, however, is only one of two: Plixer has also introduced a Security Intelligence module to Scrutinizer, which adds its own set of unique capabilities and benefits.
For more information on Scrutinizer by Plixer and how it helps network managers to gather, analyse and visualise traffic across all network connections, visit one of our previous pieces. To summarise: Scrutinizer allows network managers to gather context-rich metadata from every network connection, and analyse and visualise it to drive performance optimisations and expediently identify and resolve threats. One of Scrutinizer’s key advantages is that it does not require additional appliances, but rather integrates with existing infrastructure, adding a layer of insight and oversight – and the security and performance optimisations it provides – without adding network load.
Security Intelligence: advanced preparation
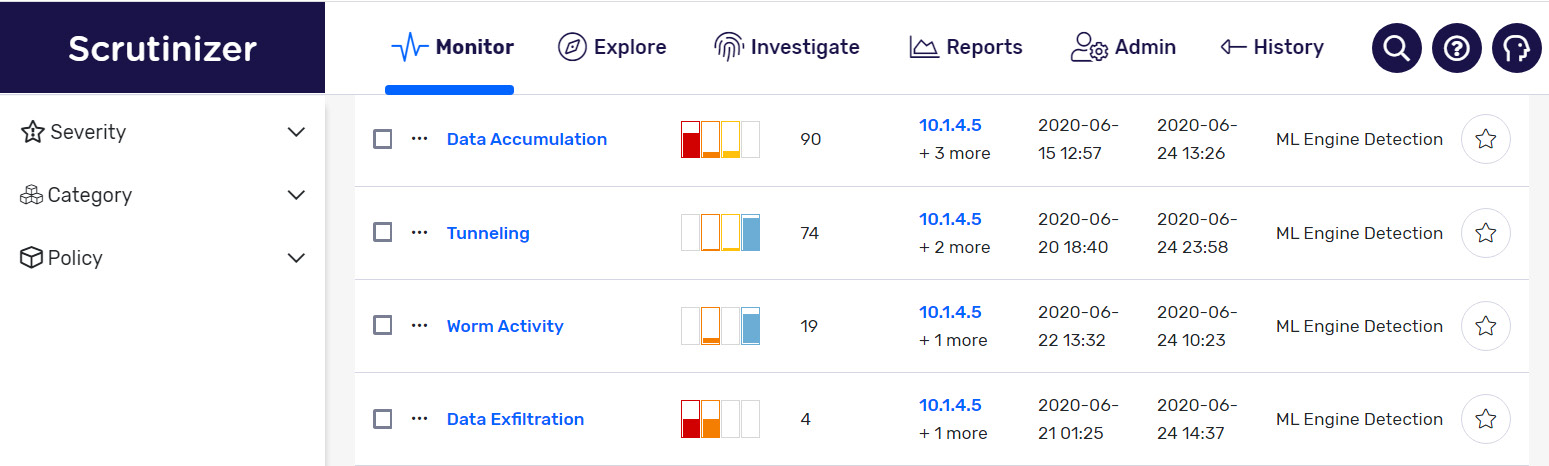
Both of Scrutinizer’s recent additions have been aimed at improving collaboration between NetOps and SecOps teams, providing equal access to insights derived from machine learning. The Security Intelligence module relieves under-resourced security teams, who work relentlessly to analyse and detect a growing list of security threats. Most security tools aren’t integrated, which leads to a daily deluge of alarms and false positives: in the end, teams struggle to determine what is real and what should take priority.
Plixer Security Intelligence uses machine learning to detect patterns from datasets that humans can’t, or, at least, are unable to do so efficiently. After, AI-based logic is applied to dynamically eliminate explainable alarms and, when the Plixer Beacon is deployed, the module is able to correlate the importance of the end-device with their risk score. This insight dictates the severity level of the incident, augmenting the team’s ability to respond to and resolve incidents dynamically and efficiently. This two-phase machine learning and artificial intelligence detection process results in advanced threat detection, and an increased ability for teams to respond and prioritise accurately.
Threat intelligence feeds – and other capabilities
Security Intelligence supports STIX/TAXII – a threat feed protocol and transport mechanism – that allows users to incorporate any third-party IP and domain threat feeds that are STIX/TAXII compliant. These feeds may come from other security vendors, or from international security teams. In addition, the Security Intelligence module allows users to historically identify when, where, and how specific domain and IP details were added into the system. Additional capabilities include the support of multiple streams’ feeds, the ability to pause or turn on/off specific feeds, and the ability to import and evaluate new intelligence feeds against existing data. Together, these offer far greater flexibility to SecOps teams: managers can determine the value of new threat sources, and choose whether or not to bring them into the solution.
Last, but certainly not least, the Security Intelligence module enables bi-directional integration with ServiceNow – allowing SecOps to streamline the process of trouble ticket creation – and the ability for SecOps to share the incident network and end-device-related data. In return, NetOps teams can share security-related data with SecOps for better collaboration. The result: faster time-to-resolution and data enrichment, reducing investigation inefficiencies.
For more information Scrutinizer by Plixer, its two new modules and the capability they deliver, contact us today.