As soon as we started encrypting data, the nature of network traffic changed. Many remember a simpler time of network management: one in which all the main protocols – DNS, HTTP, SMTP, POP – were in cleartext. Everything could be read and understood, and nothing was hidden.
Why encryption?
Encryption has enabled networks to become what they are today. You can’t have trillions of people using networks and not encrypt their activities. Encryption introduced the possibility of sustainable scalability. Networks could grow, but the security challenges of larger networks – and more diverse actors using them – could, at the same time, be mitigated.
Some resisted the transition. They questioned the ability of traditional tools to read encrypted data; suddenly, the tried-and-tested methods could not be relied upon. Managers had to adapt, tools had to evolve, and new solutions created. Those examining the challenges and limitations of encrypted data are searching for the wrong solution, by identifying the wrong problem. Encrypted data isn’t an obstacle to overcome; it’s an asset that requires us to evolve our methods.

The inevitability of encryption
The majority of Internet traffic is now encrypted. This includes streaming servers, communication servers, and the majority of daily users’ day-to-day activities. The growing use of encryption points to an obvious truth: to maintain network security, increased privacy through encryption is an inevitable necessity. As users, we depend on networks to conduct our lives. We input our sensitive information with the expectation that it, and our activities, are protected. When this basic assumption of trust and security is broken, the consequences for companies can be disastrous.
Better encryption enables networks to maintain that essential level of trust – to provide the security and privacy required by key applications. To those made nervous by the implications of this, there’s an answer: better network monitoring. This is achieved through solutions that are able to identify patterns within encrypted traffic and ‘read’ networks without reading data.
Encryption and ntop
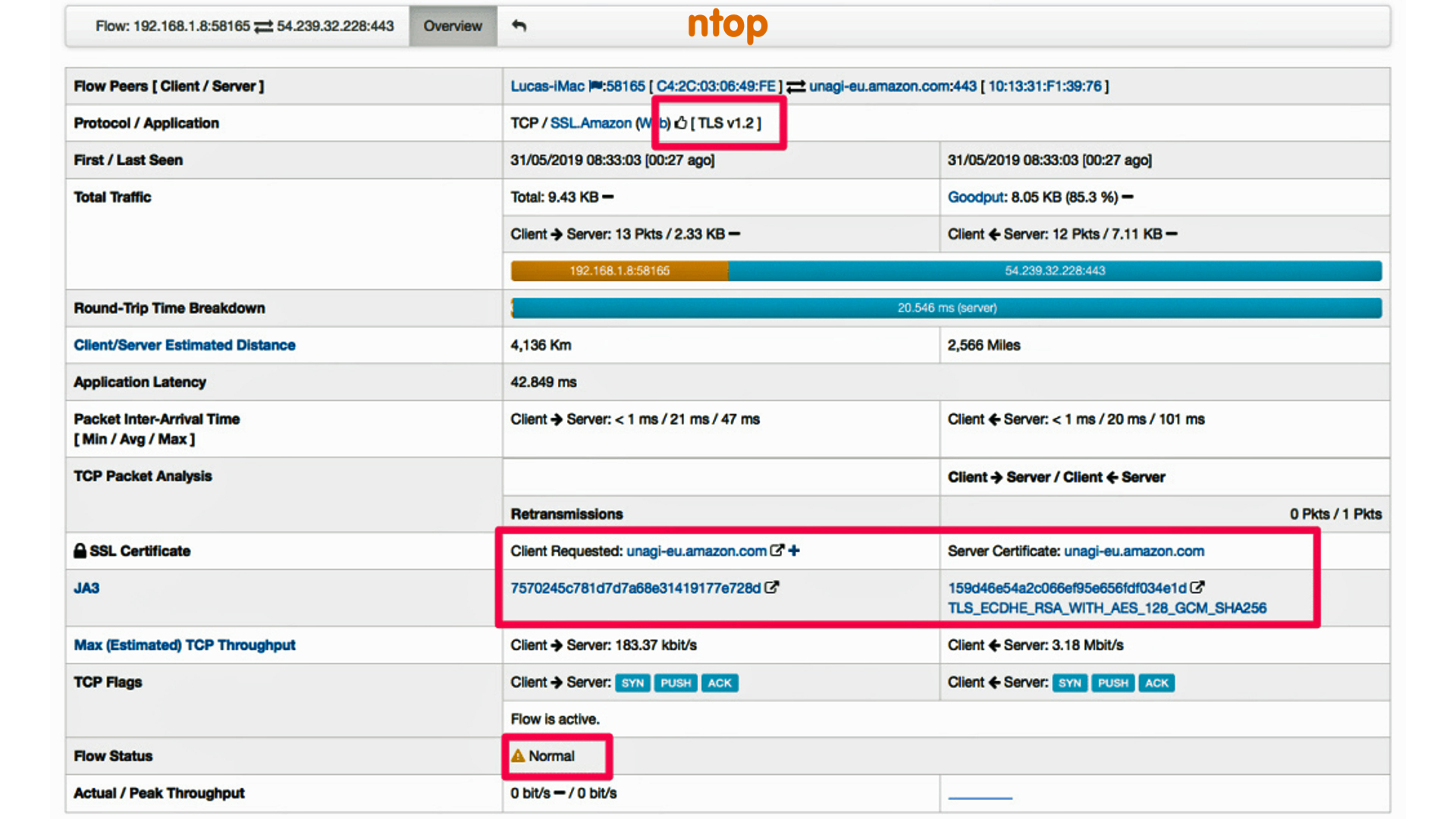
Encryption is the future of network traffic. Some solution providers have been slow to respond to reality and others have sought to pre-empt it: to provide the answer before the need and demand. An example is ntop. ntop designs encryption-ready network traffic monitoring and analysis tools to provide managers with complete traffic visibility. For their nDPI tool, this means handling encryption as first-citizen, so that managers can understand what is happening behind an encrypted connection.
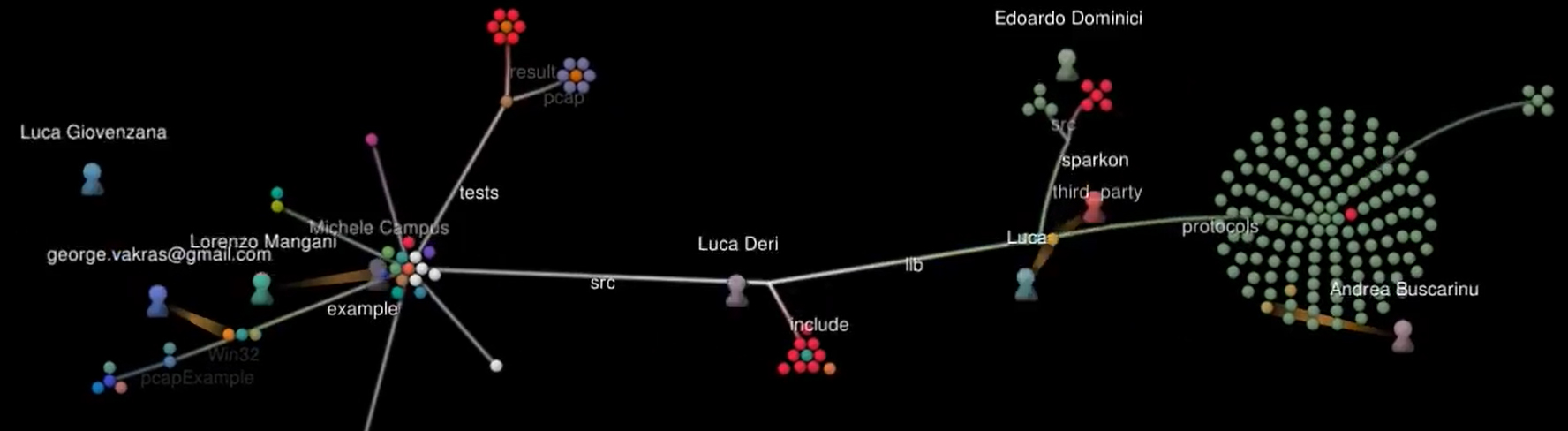
ntop’s suite of tools each offers visibility to different aspects of encrypted network traffic. Together, they include packet capture – with seamless integration with legacy applications – traffic recording, and traffic analysis. Each of these is a piece to a puzzle: they allow network managers to look beyond encrypted traffic, analyse and identify patterns and opportunities, and optimise networks with visualised reporting of data.
Encryption is change, and ntop makes that change less threatening – highlighting its enormous benefits while mitigating any loss to network visibility. To discuss encryption and how to gain better visibility into your network traffic with ntop, contact us today.