
Overnight, you had to scale out your VPN presence in an unprecedented way. Sure, after a sleepless night or two, everyone is connected via VPN, but people are still complaining about performance issues. You have no idea what applications are being used during their session and what is eating up that tunnel.
‘We got 10,000 staff remote working from home – in one weekend’ – Dylan Roberts, chief digital and information officer (CDIO) at Leeds City Council
Just the scale of the deployment that the Leeds City Council conducted is noteworthy, but how would you make sure that each remote employee is getting the network resources they need to do their job? How can you monitor application usage?
The biggest issue that I am currently seeing is that end users are using split VPN tunnels. Basically, on one side they are connected to the company’s network and on the other they are connected to their ISP directly. In this situation, we end up seeing a range of applications that really shouldn’t be on the company’s side of the tunnel.
Company policies and government regulations limit what you can and can’t do in this situation. Along with that, you are also limited to what you can see and can’t see. Sadly, this means that you don’t have the ability to throw anyone into a company timeout for using non-business-related applications, like Netflix. But you can identify what apps are being used and help your userbase, either by moving the unauthorized app to the other side of the tunnel or by creating policies that help lessen their demand on your network’s resources.
The good news is that if you are using contextual metadata, like NetFlow and IPFIX, to monitor your company’s traffic, you have this level of visibility. Since your VPN is an extension of your network, you can easily build a report that shows you what applications are being used in that tunnel, how much bandwidth they are consuming, and who belongs to that traffic.
Let me show you how.
Step 1: Filter for the subnet assigned to your VPN.

From this image you’ll notice that I am looking at my firewall and the interface that supports the VPN connection. Now I need to make sure that I am only seeing the traffic from the IPs that are assigned to that VPN pool.
In the upper left-hand side, there is a blue button labeled “Filters/Details.” Once you click on it, you will see the filters option. In the Add New Filter section, select IP Subnet and fill things in accordingly. Click the Add Filter button and update the report; now you are only seeing traffic from the IPs that are part of the VPN pool.
Step 2: We need to see things by application. 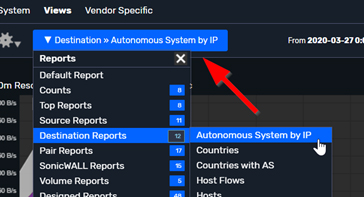
Now that we can see our VPN traffic, we want to view what applications are in use.
With Scrutinizer, you can spin to any of the available reports by clicking on the report menu. Remember, when you change to a different report, Scrutinizer respects the filters you have already applied.
To see what applications are being used, select Destinations >> Autonomous Systems by IP. Now we are not only seeing the traffic associated to our VPN pool, but also what applications are consuming that bandwidth.
Step 3: Identify the user.
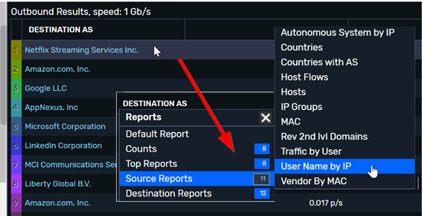 Now that I have identified a non-business application and determined that it’s consuming a good amount of the tunnel’s bandwidth, I really need to identify who is using that application.
Now that I have identified a non-business application and determined that it’s consuming a good amount of the tunnel’s bandwidth, I really need to identify who is using that application.
Again, seeing this level of flow data is simple: just click on the Application/AS name and select Source >> User Name by IP as your report. Now we can see which users are associated with that IP address. In this example, Scrutinizer can inject the session username via Active Directory integration; it’s just another way we are able to enhance your flow data.
BOUNUS: Add a threshold! 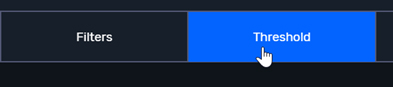
Now that we have found an application that is notoriously eating up your remote employees’ bandwidth, we really want to monitor and be alerted if and when it happens again. Since I have already built a report that shows us what applications are being used, it’s pretty simple to filter for a specific application and then add a threshold. Now I’ll know when there is an issue before everyone else!
In today’s everchanging world, we face an increased number of remote employees. Making sure that those employees have access to their day-to-day applications has taken priority. Are you looking for conversation-rich visibility along with the flexibility to integrate that data into your current environment? Why not evaluate Scrutinizer?


