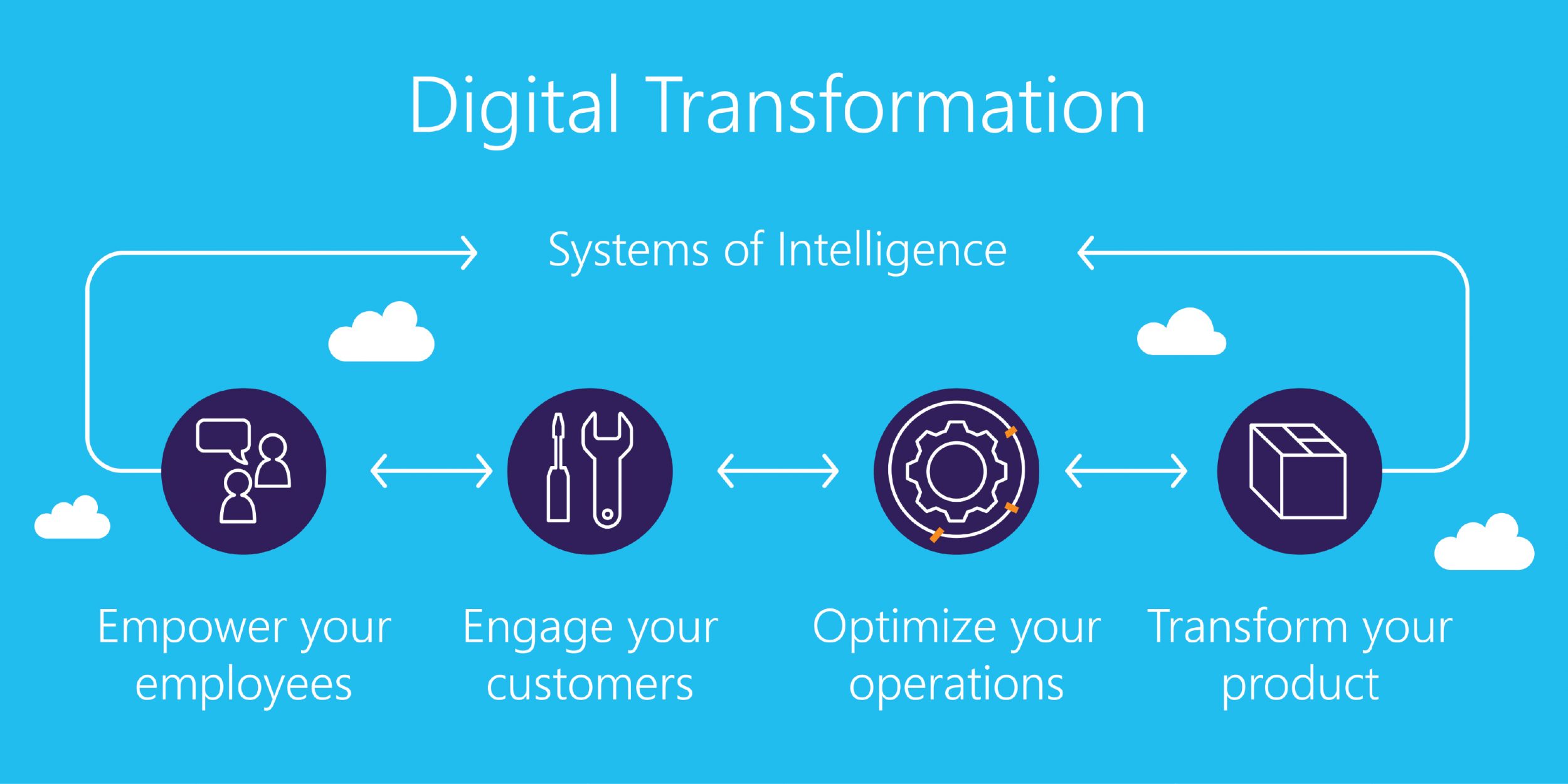
Digital transformation is on the minds of most small and large businesses. Like all buzz phrases that populate business – IoT, big data, machine learning – digital transformation is as specific as it is broad. It is, generally speaking, a strategy that promotes the accessing and integration of digital solutions to improve organizational performance and efficiency.
But it isn’t as simple as saying yes to the best new solutions. Digital transformation is an expensive and arduous process – extremely beneficial, but taxing to the staff at all levels of an organisation and, specifically, network managers. More importantly, every new solution introduced, every procedure changed, creates potential new security vulnerabilities. High-performing organisations must be backed by high-performing networks, which are more than an amalgamation of the latest and greatest. Digital transformation empowers growth, but it must be done slowly, methodically and with due consideration to the security implications of expanding network capabilities.
Making digital transformation a success
According to McKinsey, only 16 to 30% of organizations’ digital transformations have led to improved performance. We’re creatures of habit, prone to resistance, and performance boosts do not happen overnight. Once digital transformation is accomplished and the best-fit solutions sourced, performance increases as the workforce grows accustomed to the new systems and processes. In fact, there’s often a downtick in performance before there’s an uptick.
But some resistance to digital transformation is justified – especially that provided by network managers, who are aware of the security implications of rapid transformation. As employees across the organisation are exposed to new digital systems and behaviours, the likelihood for new security vulnerabilities increases. Network applications can provide backdoors into a network; an employee unfamiliar with the importance of local security protection or lacking strong credentials can compromise the network or expose critical information, including customer data.

To make a success out of digital transformation, security considerations must be part of the digital transformation strategy. They cannot arrive as an afterthought. To truly transform an organisation, it’s necessary to give employees time to adjust and acclimatise to new systems. After all, it is employees that drive an organisation’s performance, supported by software solutions.
Monitoring as part of digital transformation
Network security staff must be consulting as part of a digital transformation strategy. This is so employees can be briefed ahead of time and new security requirements considered – not least a monitoring solution. As organizational networks become more involved and extensive, and their dependencies increase, traditional monitoring can no longer be relied upon. Organisations require a dedicated monitoring solution that can extract rich information from data to offer more insight into traffic, and identify malicious or unusual activity. A larger network supporting digital transformation would normally have a significant human resource implication, but monitoring solutions – such as Securonix – make it easier to detect and resolve new incidents, including attacks, no matter where in the network they occur.
Performance optimisations must be supported by impactful solutions. It is not only the idea of digital transformation that makes it possible. It must be holistically considered, involving all parts of IT, and communicated clearly to the rest of an organisation. Monitoring goes a long way to ensure many of the security risks of digital transformation are mitigated – and it is when these transformative changes take place that the comprehensiveness of the solution matters. The more you have insight into and purview over, the better you can support your organisation’s digital transformation strategies, and protect your employee’s and customer’s data.
For more information on expanding your network’s security capabilities to support digital transformation strategies, and the solutions available, contact us today.