Experienced network managers know there’s rarely such a thing as a best-for-everything integration. When building network security capability and optimising incident resolution, the best solution is made up of multiple integrations, each specialising in a different aspect of network monitoring and analysis.
Scrutinizer by Plixer and Endace Probes
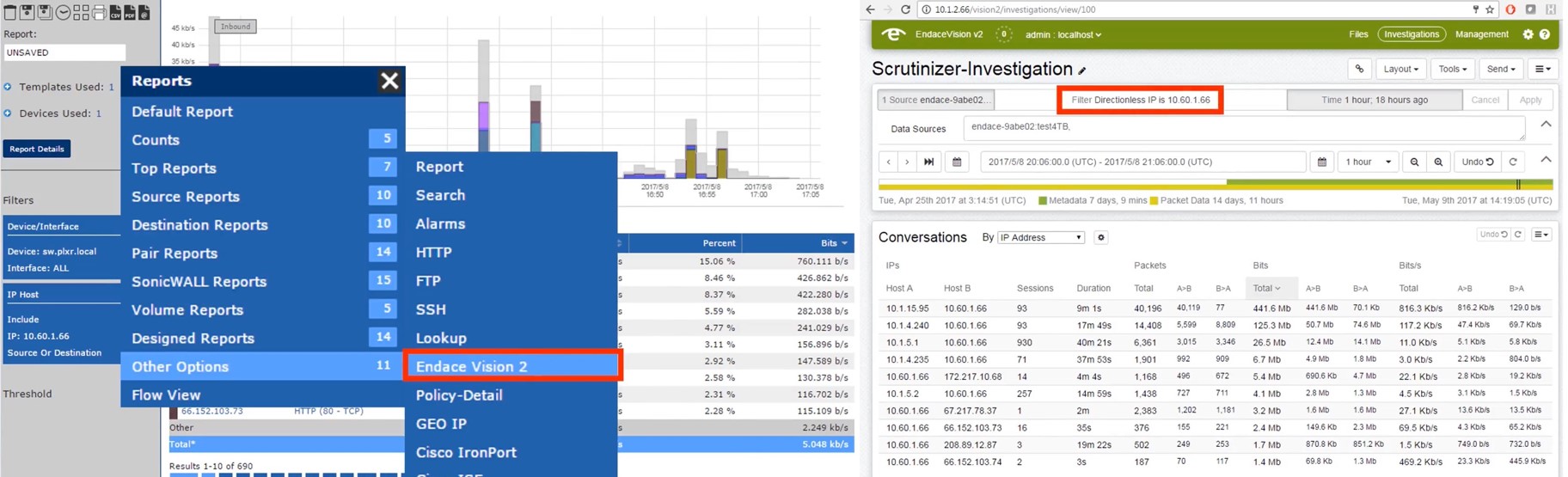
A key example of this is how Scrutinizer by Plixer and Endace Probes can be brought together to accelerate incident resolution. Scrutinizer by Plixer is a network traffic analysis system that gathers metadata from network traffic running through each connection, while Endace Vision and Endace Packets, which come standard on every Endace Probe, provide enhanced packet capture and analysis.
As Scrutinizer also features behaviour alerts – triggered when patterns are spotted in network traffic in accordance with prespecified parameters and thresholds – it can be seen as the first point of detection. Scrutinizer monitors and analyses network traffic to identify and alert, while Endace serves as a complementary resource. Endace Probe provides a virtual repository of traffic data, through data-rich packets, that offers more detailed information and expedites incident resolution. Scrutinizer identifies; Endace informs.
How it works
Alerts can be set in Scrutinizer. If, for example, a certain type of traffic has been known to be associated with malicious activity, an alert can be made for a repetition of that traffic type. Scrutinizer monitors all threats – but it’s especially useful when working from an existing knowledge base. Alerts can even be applied to the level of the specific user; a policy can be set to monitor the activities of a suspicious user and, when their activity spikes or is unusual, a subsequent alert triggered. Similarly, if an organisation has remote workers connecting to the corporate network, an attempt to use an employee’s login credentials from an unknown location can be set to trigger an alert.
Meanwhile, in the background to this continuous threat monitoring, Endace records all network traffic for later investigation. A single Endace Probe may dramatically improve your packet capture capability; placing multiple, however, ensures that all traffic that flows through those points will be understood in far greater detail, with detailed packet analysis that pinpoints the what, when and how of traffic activity.
Endace then compiles this data for an easy drill-down. If a known suspicious user has been behaving suspiciously, then a detailed history of their activity will be available. All other related traffic will be excluded; part of Endace Probe’s effectiveness is its ability to separate out incident-related activity from other network traffic, which, in turn, dramatically reduces the resource and time implications of incident resolution.
Delving further, a suspicious user’s transactions can also be viewed through the captured packets. This is visible within the interface; the information is not encrypted or otherwise inaccessible. Even a non-expert is able to understand the data, which means the information can then also be more easily passed on to a third-party.
The importance of dashboards
Each of these integrations features an intuitive dashboard. For network managers, the ability to visualise information is critical – and, in the case of Endace Probe, the easy visualisation of data means that even those unfamiliar with network monitoring are able to derive insights.
Combined, these two integrations dramatically improve the resolution pathway. Scrutinizer will immediately detect and flag a bad file download, for example, and then Endace can be consulted to understand what file was downloaded, when and by whom.
Recognising malicious behaviours is useful – but more useful is the ability to then act upon that information, which can only be done by capturing details: details which later may become evidence.
For an explanation of how Scrutinizer by Plixer and Endace Probes can be integrated to work together and provide an effective network monitoring and analysis solution, contact us today.